5. IMPROVE COOPERATION | New Info, Money, Rights, and Contracts
Previous chapter: SKIM THE MANUAL | Intelligent Voluntary Cooperation & Paretotropism
Having read the manual for civilization and analyzed previous rounds of the game, let's turn to how to make the most of future rounds in this chapter. Over the course of civilization, we developed rights, contracts and various other mechanisms and institutions to help us cooperate. But challenges remain: it is costly to search for other players to cooperate with, negotiate an agreement that is attractive to all sides, credibly commit to it, and enforce the terms once they are set. Fortunately, we can look to technologies to lower these costs and open up new levels of cooperation.
Free Information
Legal systems emerged to establish neutral rule systems that support cooperation without violence. Governments and their rules are based on jurisdictions, yet many of us no longer know or care where the people we communicate with are. The internet not only makes it dramatically easier to find others to collaborate with but it also produces a permanent system of voluntary rules that is very costly to suppress.
Free speech is a great example. Governments imprison people for violating various national speech codes. Edward Snowden is in political asylum because he is rightly worried the US won’t grant him a fair trial for releasing information to the public. Despite this, all the servers storing the released information, and all the routers transmitting that information create an emergent phenomenon by which the information stays public.
It would require global totalitarianism to reliably and permanently remove information from public availability. In the absence of that, any single entity that tries to erase widely dispersed information renders itself irrelevant, or worse, achieves the opposite of their desire; the Barbara Streisand Effect.[1]
Watch Audrey Tang’s seminar on Tool’s for Openness.
Prediction Markets
Free information is a foundational pillar of cooperation but today's information is often rather disorganized. Can we do better by supercharging how we make sense of it? Philosopher Karl Popper observed that knowledge, much as biology, evolves by a process of variation, replication, and selection. Variation of knowledge as in tossing new ideas out there, replication of knowledge as in spreading ideas, and selection of knowledge as the criticism of ideas. A healthy info system will allow good ideas to rise to the surface.
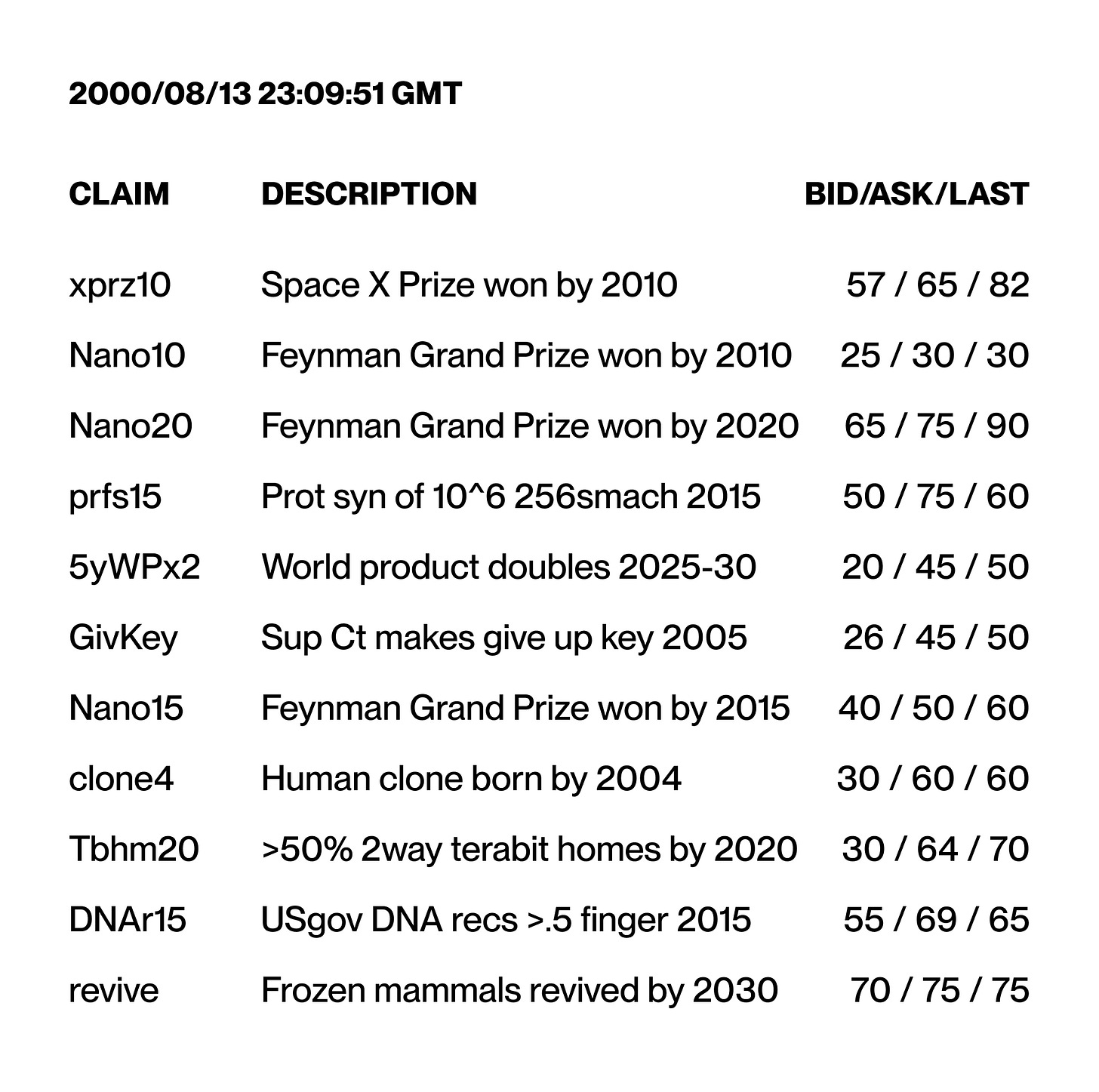
Prediction markets are such a system. Take the early market set up at Foresight’s 1999 annual gathering (screenshot below). People would contribute their expertise by opening a claim about the future for betting on a platform. For instance, “World product doubles 2025-30” tracks the likelihood of a substantial increase in world economic productivity by 2030.1 Prices represent a bet that a particular event will occur. If others believe the future price will be higher than the market indicates, they buy, and in so doing raise the consensus price. For instance, the odds for World GDP doubling were at 30-38% in 1999, moving to a more conservative 25-50% by 2000.
According to prediction market pioneer Robin Hanson, these markets can help swap our reliance on poorly incentivized experts for a market in ideas that encourages individuals to contribute their specialized knowledge: “if markets create a consensus about the value of an ownable item, such as the price, futures markets create an immediate consensus about future consensus.”
Plenty of variations are possible. Replication markets would be prediction markets that estimate the reproducibility of scientific research, reputation markets would trade in the estimated reputation of individuals or corporations and incentive markets would allow participants to incentivize actions by betting against them, making it lucrative for others to go after that very same action to prove the prediction wrong.
We can’t wave a magic wand and create a world free from interest groups trying to manipulate the information ecosystem in their favor. Instead, we can create a robust system against those forces. While we can’t assume that all problems are solvable, we should not underestimate the cleverness of games with novel payoffs for solving our problems. There will always be imperfections that an omniscient god could resolve. But the key feature of this system is that the overall direction of opinions results from the voluntary interaction of many individuals without anybody in charge. History showed that an alternative system of knowledge that could be commanded to operate in a particular way risks extremely destructive commands.
Listen to this group discussion on prediction markets on the problems they may solve.
New Rights to (Do) Things
When introducing property rights as one of the most basic institutions in the last chapter, we suggested that rights to things are really heuristics for rights to do things. But sometimes efficient rights to do things don’t correspond cleanly to tangible objects or geometric slices of the world. Our initial notion of property emerged from the game theory of trying to coordinate with each other.
Because the Earth’s crust moves slowly, we could force our notion of property onto this very naïve geometric notion corresponding to slices of the world. But there is no simple objective source of property boundaries in the physical world because physics itself has so many nonlocal interactions: If I move my arm so I am sending gravitons through your body, am I trespassing? As civilization and our desire to cooperate in complex ways grew, we advanced from geometrical slices of the world to require things like the rights of way so planes could fly over people's property, radio spectrum, pollution credits etc.
Space Property Rights
We should expect a future rich with property rights experimentation. For instance, take property in outer space: Plots of land do not necessarily generalize to bodies moving through space in ballistic trajectories. In our solar system, bodies orbit around each other and occlude each other with respect to sunlight and its energy. What if someone builds a Dyson Sphere between me and the Sun? Even if it didn't intersect my orbit, does it violate my property since I can no longer receive energy from the Sun? Determining rights in terms of orbits or radiation is clumsy and difficult.
Historical denotations of plots of land is not a bad starting point for outer space property rights. However, by starting with something physical as an initial endowment, we face substantial transaction costs when rearranging our endowments into something adapted to the activities we want to engage in.
Imagine that if you want to use a piece of radio spectrum as it passes through many plots of land, you would ultimately have to acquire it from every plot owner over that area. With property rights boundaries as vertical slices and the efficient property rights values as horizontal slices cutting through the vertical slices, this is a worst case misallocation of resources that maximizes transaction costs. Trying to get from the vertical regime to the horizontal regime by individual trades becomes extremely hard to do. For outer space property rights, we need to avoid outrageously high transaction costs.
If we discover a workable space property arrangement, it needs to be implemented with enough initial legitimacy that it isn’t immediately contested. Establishing legitimate resource claims relies on a secure title registry. We want to depend on this registry to do the right thing, not due to offered incentives, but because that is what its program requires. A permissionless blockchain might do the trick.
The blockchain, has two characteristics making it ideal for creating an incorruptible cooperation layer. First, it operates according to its stated specifications. Bitcoin is a virtual computer built out of agreement rather than physical hardware. A tremendous number of separate machines replicate the same computation and cross-check each other. While physical hardware may have security trap doors, if a quorum of many different algorithms that don’t trust each other agree on a transaction, this is a credible machine to run our computation on.
Blockchain’s second innovation is that it provides an agreed message order. A single piece of arbiter hardware can implement censorship by deciding to never see a message it doesn’t want to accept. In contrast, at least for proof of work, messages coming into the blockchain are coming into the memory pool, the transactions waiting room, and are visible by the blockchain’s miners. The miners compete to gather the messages into a block and publish them. This avoids the problem of double spending, which is fundamental to currency creation, something we'll discuss next.2
For registering space property rights, it is the combination of the blockchain’s ability to act according to the stated specifications and to reliably service requests, that makes it a candidate for creating incorruptible institutions. Knowing it’s the internal logic that makes it function reliably lets the rest of us incentive-align around it.
As long as there is no competing governmental title registry for the resources, claims on this title registry blockchain could be created without an opposing claim. There might be little interest in abolishing its legitimacy and much interest in upholding it. Suddenly, there are space property rights where previously there were none. Everyone is now either better or similarly off as in the absence of the registry. It's not impossible that establishing a blockchain-based system for space resources starts off seeming so unreal to people that it can grow to substantial legitimacy without competing government claims to the same resources.
Watch the seminar on Legal Considerations for Space Property Rights.
Reliable Money
The legacy monetary system comes with a plethora of pathologies: Robert Mugabe can print endless cash, inflating away the savings of Zimbabwe’s citizens. Vladimir Putin can freeze an NGO’s bank account, and refugees can get locked out of the banking system. Situations such as Operation Choke Point, when the US government used its control over banks to shut down unquestionably legal businesses, or when credit card companies blocked payments to WikiLeaks, show democracies aren’t insulated from these problems either.
Fortunately, Bitcoin happened. Built on the blockchain, Bitcoin injects internet properties such as programmability, interoperability, and composability into monetary value exchange, while guaranteeing its own scarcity. Bitcoin is a great example of a new layer of rules built on top of the internet’s permanence. We can think of its rules as a constitutional system for the digital jurisdiction, so that the web’s information economy can now operate within it. It directly threatens what offline jurisdictions consider their prerogative; minting money. Nevertheless, it succeeded at providing the world with a currency that is very costly to corrupt, even for governmental jurisdictions.
Because crypto offers a cross-jurisdictional, censorship-resistant exchange medium, it is not only attractive for people lacking access to institutions, but also for those who distrust them. It allows anyone to store, send, and receive money without asking permission and without proving one’s identity. Over half the world’s population live under an authoritarian regime, and could stand to benefit from this. In Nassim Taleb’s words, it offers an “insurance policy against an Orwellian Future”. Simple money is the most obvious high-leverage institution needing public non-corruptibility and our initial success is encouraging here.
Private Transactions
Bitcoin gives us monetary sovereignty. But Bitcoin, and almost all existing cryptocurrencies, put all transactions on an open public ledger, readable by anyone anywhere. Ethereum, and most blockchains that support smart contracts today, do all their contract execution on an equally public ledger. Although participation is said to be anonymous, in practice it is easy to do traffic analysis, a form of statistical reasoning, to correlate blockchain activity with players in the physical world. The tools for doing traffic analysis are quickly becoming a commodity. Because blockchains are immutable, malicious actors have lots of time to learn more about our activities.
Blockchains without strong privacy, i.e. most blockchains today, create dangerous new opportunities for real world crime. If real-world commerce moves onto such blockchains, private agreements would be near impossible. So-called rubber hose attacks and kidnapping come immediately to mind. Besides individual criminals, we should also worry about corrupt governments or interest groups engaged in human rights abuses or blackmailing.
Innovations like zero-knowledge proofs make it possible to encrypt transactions fully, while still allowing them to be verified via consensus. Blockchains with privacy would deny anyone the information needed to figure out who to attack. Currently, this level of privacy is available for cryptocurrency but not widely used. We should make it the default.
Check out this seminar on Zero-knowledge enabled Cooperation.
Complex Contracts
Complex play can emerge from simple rules. Through commerce we gradually figured out how to use contracts to bind ourselves to complex games. Right of contract states that voluntary arrangements between consenting adults should be allowed because they allow adults to find novel ways to cooperate.
To cooperate between mutually suspicious parties, we mostly rely on legal contracts. Contract enforcement is expensive and most disputed commercial relations are well below the threshold for going to court or arbitration. This limitation creates barriers. Unless we are rich enough to take everything to court, complex forms of cooperation are restricted to those we trust and have long-standing iterated relationships with.
Being members of the same jurisdiction somewhat reduces risk since operating under the same law lets us assume each other will behave well. The internet enabled the novel opportunity to create a website and cooperate with millions of total strangers. Still, on the internet, you might engage with someone who is completely anonymous. Some cyber attacks are committed in jurisdictions where the attackers aren't subject to punishment.
The result is that cooperation among strangers at a distance is restricted to simple interactions, such as giving away information for free. Even taking payment in exchange for something, a rather simple deal in itself, is often enabled by third parties such as credit card companies taking on the transaction risk. Our ability to cooperate richly with the majority of the world whom we don’t know still remains underdeveloped.
Smart contracts could change this. They were conceived by Nick Szabo in 1996 to automate contract execution by embedding it "in the hardware and software we deal with”. Smart contracts are contract-like arrangements expressed in program code, where the program’s behavior enforces the contract’s terms. They create automated arrangements to which we bind ourselves by placing rights into escrow with the contract. These rights are only released back to the contract participants according to the agreed contract terms.
Lawrence Lessig suggests we can achieve a particular end through different means, with legal contracts being one and computer code being another. Having only been able to build cooperative arrangements whose execution relies on human beings, we struggled to insulate them from human corruptibility. Smart contracts significantly increase the range of possibilities for what computer code can achieve. This makes cooperation reliable, credible, and trustworthy to an extent never achievable when institutions had to rely on human beings to function.
Ethereum, a general purpose blockchain, was the first real-world system to establish a sound, smart contract architecture. With Ethereum as a precedent, we now have a user-extensible rules system in which every contract is a new set of rules that cannot be shut down. Rather than being the last invention of this new level of the game, we should think of smart contracts as a key to unlock the next levels.
Reusable Templates
In the past, making attractive printed materials required going to a print shop. With the advent of laser printers and the Macintosh, suddenly regular people could create and print attractive designs at home. What followed was a lot of horrible-looking newsletters with tremendous overuse of fonts. People had yet to develop the skills to best use their new tools, so demand built to improve them. Early desktop publishing programs evolved with templates guiding users away from using Comic Sans for everything.
Similarly, our cooperative arrangements are currently crafted by highly specialized, highly paid lawyers. They are supposed to be good at writing contracts that don't fail in unexpected costly ways. Most of a legal contract is actually about how to deal with a variety of failure cases and pathological contingencies that a layperson never would have thought of. Early smart contracts will have effects no party would have wanted if they anticipated them. It takes time to develop tools and templates that embody expertise about unintended consequences and contingencies. Just as early, awkward design efforts evolved into today’s slick templates allowing anyone to create sophisticated publications, automated contracts will evolve from clumsy, costly proofs of concepts to ever more sophisticated plug-and-play templates.
While code for smart contract templates is expensive to create the first time, it can be reused indefinitely. The more smart contracts are used, the more they get play-tested with regard to unintended consequences so that we can rely on those that prove robust over time. As the ecosystem grows, so will the demand for improved skills. Those who improve first can create templates and tools to benefit the rest of us. JavaScript already delivers a secure and easy-to-use toolkit that empowers non-expert programmers to write simple smart contracts that can be understood by non-experts. Equipped with the ability to enforce rights and responsibilities in code at low cost, people across the world are empowered to exchange, trade, and cooperate in new ways.
Split Contracts
Not everything can or should be automated. We may never be able to flawlessly represent our intentions in legalese or code without risking an outcome not reflecting what we actually wanted. Dumb paper contracts lock in states without knowing what future participants will consider relevant. Lawyers try to freeze the next 10 years in hard-to-parse prose, only to litigate when the contract fails. When writing a contract, we are writing interaction rules for an unanticipated world. We face an alignment problem among current and future parties. An open contract is a plausible alignment strategy.
Rather than litigating and blaming when predetermined contracts fail, open contracts would let parties embrace change and improve the game’s next iteration. Often we will want to rely on a human at crucial steps to negotiate future parts of an agreement chain. They could take into account information from previous rounds and consider new circumstances when initiating the game’s next iteration. Preserving a human in the loop can be a useful feature. Sometimes we don’t just want the automated contract to be the only credible commitment. Instead we want the credible commitment to account for factors that require human judgment.
A Split Contract would divide the contract into two parts: the automated part directly enforced by software, and the prose humans interpret in the case of dispute. If either party decides to dispute the contract’s automated part, pre-chosen arbitrators judge the disputed terms and may overrule them. This has two advantages:
First, the contract terms are fine-grained; specifying the amount paid upon committing to the contract, the amount paid upon delivering the answer, and the amount paid when agreeing it satisfies her criteria. Dumb paper contracts leave the default situation determined by the asset’s default location. By escrowing money, the contract changes this default distribution. In Nick Szabo’s terms, from possession being 90% of the law, we move to behavior becoming 90% of the law. By rearranging the burden of initiating a dispute, both parties get skin in the game to comply.
The second innovative feature is the fine-grained negotiation process for the contract terms. Payment amounts, prose text, and arbitrator selection are left up to the discretion of the contractors. By co-negotiating those parameters upfront, they can make expensive dispute resolution less likely. We dispute a contract hoping we win, but it carries some expense and risk. The obvious cost is that human arbitrators are expensive, but a more subtle one is uncertainty. If we don't dispute, we are stuck with a disliked, but known, outcome. Yet, once subject to the arbitrator's judgment, the result is less predictable. If we could have predicted it, we could have written a more mechanical prediction into the contract in the first place. Reducing the odds of a human dispute in the first place is a great hack for reducing enforcement costs.3
Watch this seminar on Split Contracts and Decentralized Arbitration.
The Ancient Technology of Reputation
Mixed Contracts combine the best of contracts with reputation. To see the value of reputation, let’s compare our consumer relationships to an iterated prisoner's dilemma in which a producer is defecting on the arrangement by selling a worthless product. To retaliate in the next round, we must notice this defection and decide to warn others away. Since this process is expensive and we frequently find ourselves in non-iterated games, reputation agencies have evolved. Reports by consumers put the producer in an iterated situation with the community as a whole while trademarking establishes valuable long-term producer reputations.
Reputation, if paired with contracts, can help create entirely novel arrangements. Crucially, such a reputation system could also work if Carol maintains pseudonymity. If a negative reputation system is one where participants avoid entities with a bad reputation, a positive reputation system is one in which participants seek out those with a good reputation. Pseudonyms are problematic for negative reputation systems, because it is easy to let go of a negative reputation by switching between pseudonyms.
Positive reputation systems can still succeed as long as no one can claim another’s identity. Imagine pseudonymous Alice and Bob would like to draft up a contract that relies on legal enforcement. Let's say Alice also has a contract with Carol, so she is subject to legal enforcement that is invisible to Bob. Carol can assure Bob that she has enforcement powers, since she knows Alice’s real identity. If she is reputable enough, this may assure Bob even if the specifics are opaque to him.
If Carol wants to continue being consulted for arranging deals between the Alices and Bobs in this world, she will make sure that she can honor her part of the contract. This role is similar to the role credit card companies played in enabling today's e-commerce. The demand for reputation information may eventually provide a market for pseudonymous reputation services, analogous to credit rating agencies and consumer experiences.
Check out this seminar on Blockchain Governance.
A New Menu of Organizational Choices
When starting a new organization, today's laws constrain founders to choose from a menu of confusing options ranging from a for-profit to a classic non-profit 501(c)(3), with several organizational types in-between. The combination of court cases and legislative compromise that led to the particular combinations available in each state is so complicated that only a lawyer can untangle them. They solidified in a very different past from our modern world, dating back to before the World Wide Web.
Compare this to a Decentralized Autonomous Organization, aka DAO. It’s a network-native entity with no associated central management and its own asset pool. Smart contracts between the organization stakeholders may decide how to use the assets. Through DAOs, people can participate in many new organizational structures that distribute reputation or money according to value contributed or make decisions via the wisdom of the crowd. It is very costly for people within the organization to prevent the relevant set of immutable smart contracts from executing as specified. Because they run on a blockchain with international nodes, these contracts are more resistant to internal and external corruption. This makes them an excellent candidate for experimenting with previously unthinkable cooperative arrangements.
DAO templates, pol.is voting systems, and other emerging tools could equip the rising tide of internet communities with collective ways to pool assets and govern over them to pursue shared goals. Many experiments will fail but we only need a few successes to create an entirely new menu of organizational choices. After all, current institutions are also made of contracts.
Watch this group discussion on Decentralized Autonomous Organizations.
Collective Action Problems
The world is full of possibilities we all would like to see realized, but no individual has an incentive to contribute to. This is especially true if we think we can benefit without contributing; the classic free rider problem that is at the root of the world's nastiest collective action dilemmas. But what if, instead of worrying that a small contribution won’t make a difference, you could ensure that it does? Kickstarter allows you to pre-commit to fund the open source project of our choice if and only if enough others commit to do the same to reach a critical threshold. If we all want an outcome enough, we can often move there via assured agreement. If not, no action takes place and any committed funds are returned. Such Assurance Contracts are great tools for solving large, multiway group commitments.
Dominant Assurance Contracts
A problem with assurance contracts is that even with minor transaction costs there is too little incentive to contribute. Imagine an open source software improvement costs $800 to fund and is worth $100 to each of 10 people. If each person pays $80, they get the results and are all better off. But each person may choose not to donate because they may still benefit from the software bug fixed, even if they don’t contribute. If you think that no-one else will contribute, it’s rational for you not to contribute; however, if you don’t, then why would anyone else? Not contributing can quickly turn into a self-fulfilling prophecy.
A creative solution, introduced by Alex Tabarrok, is the Dominant Assurance Contract. It’s an assurance contract with the added condition that if the funding benchmark isn’t reached, the sponsor must pay a prize to the pledgers. Pledging now becomes a dominant strategy, or in Tabarrok’s words, “a no-lose proposition—if enough people pledge you get the public good and if not enough pledge you get the prize.”
Listen to this seminar on Dominant Assurance Contracts.
Quadratic Funding
Another potential solution to help with the free-rider problem of public goods is Quadratic Funding. By pledging even small amounts to desired goods, participants can direct the relative funding amount of external entities which agree to match the funds. The trick is that matched amounts are calculated by using the quadratic funding formula. This is where the amount a project receives is proportional to the square of the sum of the square roots of received contributions. Matching sums are based on the number of supporters, not the amount donated. This creates strong incentives to give even a little, ultimately countering incentives to free-ride.
Retroactive Public Goods Funding adds to this the layer that it’s often much easier to agree on what was useful rather than what will be useful. By rewarding public goods projects that were successful, it can incentivize their creation. Such experiments are at an early stage but, if successful, they can create what Vitalik Buterin calls “a general purpose infrastructure for funding public goods in the same way that money is a general purpose infrastructure for funding private goods.”
Chapter Summary
Various costs prevent us from cooperating creatively. It takes time, energy, and money to find each other, bargain an agreement, and enforce it. If only we could lower these costs, cooperation could be rich. The digital realm provides new arenas to reinvent cooperation. New media, property rights, and contract experiments are just the tip of the iceberg. Most of these experiments will fail but the few that succeed may usher in a new era of cooperation. It’s hard to see how to get there from here. In the next chapter, we’ll take the first steps.
Next chapter: GENETIC TAKEOVER | Cryptocommerce
Thank you to Chris Hibbert, who coordinated and maintained the market.
Miners have opportunistically delayed a message before. We should think about better approaches to that danger, especially as mining is increasingly centralized in a few Chinese nodes. Nevertheless, blockchain still bounds the problem. A message cannot stay censored for long because of its content, given a competitive market of miners. So even though there is some corruption opportunity on the edge, such as to front-run, the messages should always get serviced reasonably promptly. Pre-crypto, perhaps our best hope at creating trustworthy money was via competition and reputation feedback. But relying on reputation is insufficient; reliable operation of money matters most in emergencies when stressed people make compromises regardless of their reputation. Bitcoin, and a growing number of crypto alternatives, are doing something better. By examining its internal workings, we know that the money itself operates in an incorruptible manner, regardless of external pressures.
AMIX, The American Information Exchange, shown below, was an early prototype of a Split Contract. Designed back in the 1980s before the web browser, it was a computer-mediated market for matching information buyers and sellers. Up to then, finding information on a topic involved fishing for relevant bits of knowledge from the sea of newspapers, TV, journals, and books. AMIX replaced this random walk with a targeted market on which you could ask questions and those with relevant expertise could sell their answers. Barbara, an early AMIX user, wanted to hire a consultant to figure out if it makes sense to build a co-working space in Palo Alto. She defines what would count as a satisfactory answer and uploads the request to the exchange. If a consultant delivers an answer and thirty days go by without Barbara taking any action, the automated contract would pay him the full amount. To stop the payment, Barbara would have to explicitly state his document does not meet her terms. The contract would then take those contradictory propositions to the arbitrators. They would only get to overrule the amounts paid on accepting the document. Meanwhile, with paper contracts, the consultant could have given Barbara a perfectly fine document. She could refuse to pay, leaving him with the expensive legal action to get what she owes him.


Decentralized in theory is not decentralized in practice. See:
https://blog.mollywhite.net/blockchains-are-not-what-they-say/
I'm enjoying myself...knowledge embedded.